What regulations for data protection in the financial services industry may apply to your fintech application? How should software developers secure the apps’ code? What is AES? How to promote security at the enterprise level? Keep reading to learn the answers and tips on fintech app security solutions.
Table of contents
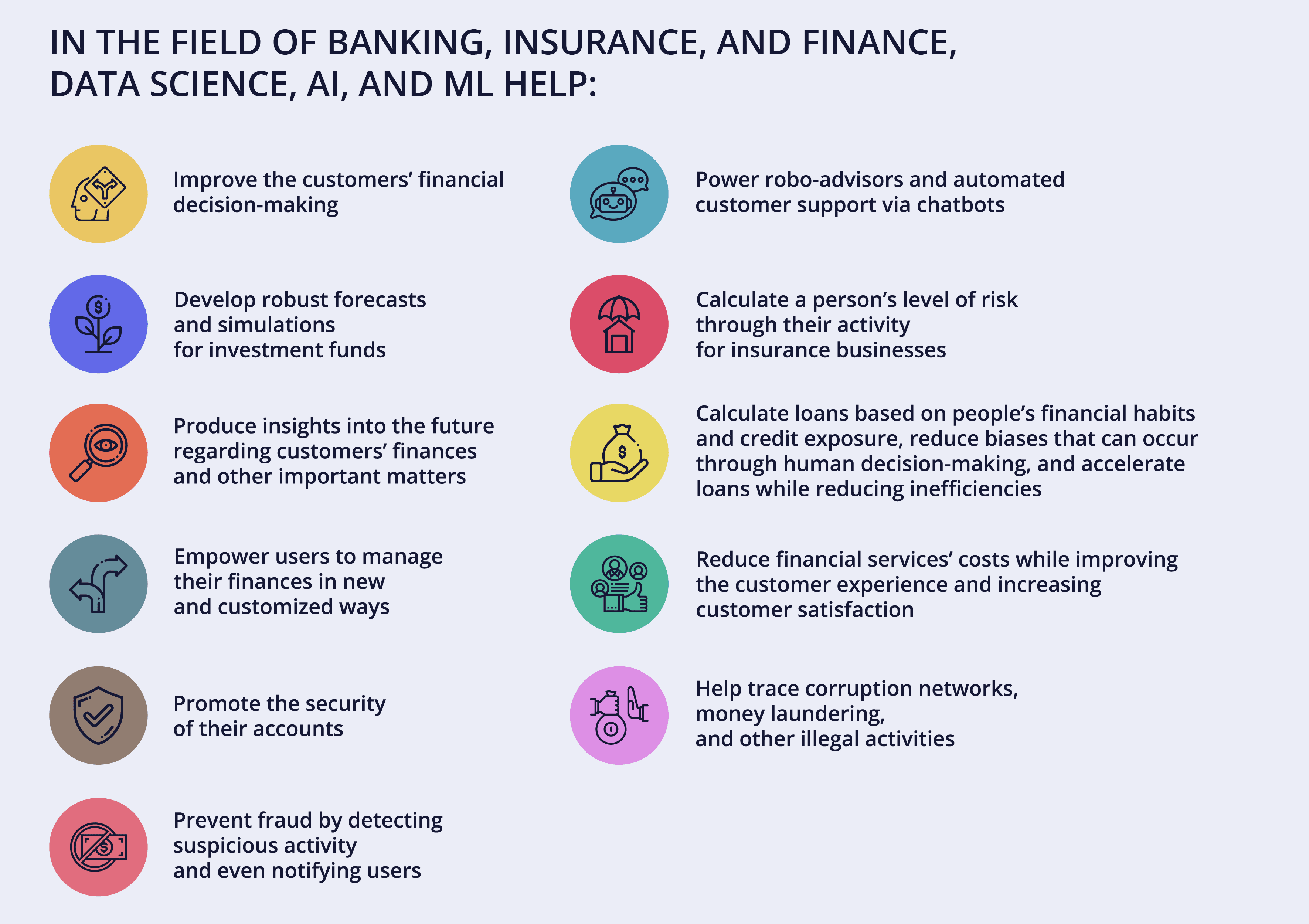
According to the Fortune Business Insights’ 2023 report, the global fintech market size, estimated at USD 294.74 billion in 2023, is predicted to grow at a CAGR of 17% over 2023-2030. It is driven by the exponential growth of e-commerce, the increasing popularity of digital payments and mobile banking, and active incorporation of artificial intelligence (AI) and machine learning (ML) in financial technologies.
Learn more: AI-Powered Banking: Transformative Trends, Insights, and Use Cases
This makes fintech attractive for both startups and cybercriminals. Financial services companies deal with highly sensitive personal and business information, but their data storage issues, cross-platform malware contamination, data leakages, and other vulnerabilities often jeopardize that data.
The average cost of a financial services data breach is 5.97 million USD. Startups face a higher risk because they often lack the human and capital resources to manage their financial app security challenges.
The good news is that companies can follow certain fintech app security best practices to prevent many breaches. App development focused on data protection is a hallmark of a reliable and trustworthy financial services company and gives it a competitive edge. The whole company’s existence may depend on this.
Read also: How Onix Organizes Your Software Development Process
Let’s start by reviewing some of the security challenges that fintech organizations face worldwide.
Primary Challenges to Fintech Application Security
Digital identities
An identification, authentication, and authorization system should safeguard an app against any intrusion or suspicious activity. Still, password-based and even two-factor authentication (2FA) may be vulnerable to cyberattacks.
Data ownership
Fintech companies need robust mechanisms and procedures for regulating who can access, create, modify, and delete their data. Data ownership, i.e. the possession of and responsibility for data, requires the knowledge of multiple technical and legal processes and compliance with applicable state regulations and standards.
Fintech systems’ vulnerabilities
Hackers can exploit system weaknesses to access sensitive information. Unfortunately, most companies aren’t aware of the attacks and data breaches in their systems until it’s too late. The increasing use of gadgets and IoT devices complicates the management of these vulnerabilities.
Involvement of third-party services
Integrations with popular payment gateways, analytics systems, social networks, or chatbots can compromise the security of fintech apps. Hackers may use third-party access to replicate a legitimate user and access the system.
Cloud migration
Many fintech companies have moved their operations onto cloud services for better performance, scalability, and cost optimization. However, the complexity and load of transactions in different cloud environments can complicate fintech data protection and supervision. The integration of yet another technology may create more vulnerabilities.
Malware attacks
Malware attacks remain the prevalent type of security threats to financial organizations.
Human errors
Human error is the main reason for successful phishing attacks. Lost or stolen devices also provide opportunities for cybercriminals.
Compliance with regional and international data protection regulations
Depending on a fintech company’s location and targeted markets, it must comply with different regulations in the financial services industry. Otherwise, a fintech app risks isolating itself from specific markets. Moreover, non-compliance may cost millions in lost productivity, business disruption, fines, and penalties.
Here are some of the regulations and standards you may have to follow:
- Payment Card Industry Data Security Standard (PCI DSS) for all entities that gather, transit, or store credit card information
- ISO/IEC 27001, another international certification that needs to be implemented for fintech security
- General Data Protection Regulations (GDPR) for all companies that provide financial services in the European Union and the European Economic Area
- The revised Payment Services Directive (PSD2) that regulates electronic payments and cross-border transactions in the European market
- Regulation on Electronic Identification and Trust Services (eIDAS) that provides a legal environment for interactions between fintech organizations, businesses, governmental entities, and citizens in the EU
- Financial Conduct Authority (FCA) for financial firms providing services to consumers in the United Kingdom
- Good Practice Guide 13 (GPG 13) for all British government systems and networks, vendors, and outsourcing companies
- Act on the Protection of Personal Information (APPI), if your fintech app handles private data of Japanese residents
- Personal Information Protection Act (PIPA), for entities dealing with private data in South Korea
Fintech solution developers need to manage both regulations compliance and data security issues throughout the software development process.
Read Also: The Importance of Data Security in Healthcare Software
The following solutions and best practices can help your company address these challenges, build a compliant fintech product, and protect your customers’ and your business’s valuable data.
10 Tips for Financial Services App Protection
1. Recruit the right product development team.
The security of fintech apps is the collective responsibility of the financial company’s security officers, management, software developers, and others. Regarding developers, experienced specialists well-versed in fintech security standards, regulations, and technical means to ensure compliance and data safety are the best choice.
When recruiting specialists for your team, hiring remote developers, or outsourcing the development altogether, learn about the services they provide and examine their website, portfolio, clients’ testimonials, and any other proof of expertise in fintech app development.
Namely, the candidates should have expertise in the following techniques that promote security for financial apps.
2. Ensure the app’s secure architecture and code.
Building a secure fintech app’s logic means integrating security into every step of using the app. At the early stages of your finance app development, you need to consider what data to store, where it will be saved, who will have access to various app features and data, and more.
Try to keep it simple. Bad guys can't steal sensitive information from your system if it isn’t there in the first place. You'll want to store only the minimal crucial data.
For instance, it’s possible to carry out payments without keeping the customers’ payment card numbers.
Secure code is the backbone of a fintech application. If your code has even the smallest vulnerabilities, your entire business may be at risk. Securing your software code includes securing the architecture, design requirements, code optimization, and efficiency.
The software architect and the developer who designs the code should consider input validation, authentication, passwords management, cryptography practices, proper logging and handling of the errors, and secured communication.
Every app identifies each user as the one that is either permitted to perform specific tasks or not. Your software is going to have functions accessible only to a few persons. Varying access levels can preclude unauthorized employees and customers from accessing your corporate information and the customers’ data. You will need a system for setting up user roles and organizing permissions.
Role-based access control (RBAC) restricts access to the software and network based on a user’s relationship to the organization. For example, a fintech app may imply the following roles:
- Administrator
- Manager
- IT specialist
- Online support staff
- Customer
Each user will have access to data and processes pertaining to their role and profile and will be restricted from other parts of the system and sensitive data within the enterprise.
Access control list (ACL) is an alternative system. This model lists all the actions a particular user is allowed to take.
The following practices are recommended when it comes to ensuring your fintech code security:
- Before putting together your fintech app, clearly define access control rules, including insecure IDs, file permissions, and client-side caching. The team needs to follow the adopted policy strictly.
- It’s best to limit every user’s rights to the necessary minimum of actions and commands. The most secure way is to deny access to all app functions by default and allow it only on a need-to-need basis.
- Identify the sensitive data you will deal with and how you’re going to protect it. (Some of the recommended steps will be suggested further in this article.)
- If there is a need to send some data to external networks, make sure it is the necessary minimum. Review it periodically to prevent any confidential information from being transferred as clear text.
- Input validation will prevent intruders from injecting your app with malicious code by either sanitizing or rejecting that input.
- Encourage the developers to leverage tools and frameworks with automated security mechanisms in place and to pay attention when they detect any flaws in code.
- The team should scan the source code rigorously and regularly test it for vulnerabilities. They should create robust algorithms that will help detect any flaws in the app’s code.
- To prevent hacking via SQL injection, it’s worthwhile to simulate attacks on the app and see whether they were successful. It’s vital to install the latest updates and apply security patches as soon as possible.
- Regularly consult with OWASP: they publish some of the best articles and documentation on web security.
The code should be agile and easily portable between different devices and operating systems. This enables software engineers to act and update code promptly in case of a data breach or attack.
Choosing a technology stack for your product is also important. Besides security, it has to facilitate the product’s reliability, scalability, and maintenance.
Read more: Intro to Feature Flags in Java Using the Spring Boot Framework
3. Use code obfuscation.
Cybercriminals can create clones of fintech apps to collect the personal data of misguided users.
Fintech companies can use code obfuscation to protect their apps from cloning. The process may include encrypting some or entire code, stripping out potentially revealing metadata, naming classes and variables with meaningless labels, or adding unused or meaningless code to an application binary.
Such obfuscation makes it difficult for hackers to analyze the app’s code and understand the work of its algorithms, let alone decipher or replicate a designed software code.
If someone tries to steal your code, they will have to deal with its obfuscated version first. This will discourage some casual hackers who aren’t ready to put in much effort. Others will have to overcome a major hurdle to reverse-engineer your original code.
Code obfuscation also helps protect fintech solutions against unauthorized access, vulnerability discovery, trade secret theft, and bypassing licensing.
4. Build secure identification, authentication, and authorization processes.
Identification relates to entering a name or username when a person claims to be a user of your app. Authentication should prove that they are who they are. After the system has identified and authenticated them, the next step is to determine what they are authorized to do.
Your team should design each step with special care. The trick is in enabling users to complete the authentication rapidly and with minimal effort without compromising security.
Passwords are still a popular authentication method. Basic safety parameters, such as enforcing at least 14 characters in length, mandatory use of special characters, password expiration, etc., are a must for apps with financial transactions.
Still, these credentials can easily be stolen or hacked. For instance, mandatory change of passwords every 2-6 months is problematic. Customers and employees may end up updating or reusing old passwords, making it easy for hackers to guess the patterns and hack their data.
Many fintech data security regulations require multi-factor authentication (MFA). In this process, users requesting access make two or more claims to prove their identity, and the system has to verify all these claims before giving access to the service.
Fintech companies should implement at least two-factor authentication. One common mechanism involves sending one-time code either through SMS or email. Push notifications that allow users to verify their identity with a single touch are another 2FA method.
Banking apps use biometric identifiers, e.g., thumbprint or facial recognition, to validate customers when they log in or authorize in-app transactions, replacing PINs, passwords, and digital signatures. Such biometric authentication enhances both fintech mobile app security and user experience. Adding these biometrics, retina scanning, or voice recognitions may also reinforce the traditional username and password-based mechanism.
Learn more: How to Start a Neobank in 2024
Major fintech companies also use risk-based or adaptive authentication. The system may analyze the geolocation, registered devices, connection type, time of access, typing biometrics, and other behavior details of the person requesting access to detect any suspicious activity.
It’s also helpful to limit the number of users’ attempts to sign in and track failed attempts. It can help to detect and thwart hackers before they succeed in entering the system.
Upon authentication, an API may allow certain users to complete specific tasks and issue certain commands while restricting their access to other areas. Some common authorization methods include route assignments, bandwidth traffic management, and IP filtering.
It’s also beneficial to limit the duration of a user’s activities in the app. It should automatically log them out after a certain period. A shorter session lifetime reduces the risk of malicious access to your fintech data from an active session. Even if a hacker gains access to the account, they will have limited time to capture valuable data.
Ensure an appropriate security authorization level by setting up a user management engine. The user management console can list all actions and display all permissions given to access specific objects.
Dynamic PINs or one-time passwords (OTP) can provide an extra layer of protection each time a user wants to complete a transaction.
5. Log everything, analyze, and act accordingly.
Fintech app owners need to be able to monitor all transactions and stop hazardous ones.
It’s recommended to keep systematic logs of user activities. The system should continuously record at least every user’s ID, IP address, device data, geolocation, and their actions and transactions in the app.
All transactions can be labeled as low, medium, or high-risk. You can utilize your own fraud scoring methods or combine them with third-party solutions. Suppose a high-threat level transaction is being initiated. In that case, the system would automatically decline the query, pause the activity, and notify the employees in charge.
It would be helpful if the system requested approval from several persons before a critical action, such as a large transaction or modifications in crucial information, can be executed. The choice between sequential and parallel approval flows may depend on the business process. This method helps reduce the risk of mistakes or deliberate attacks.
Major banking apps and financial services incorporate payment blocking features into their apps. Such mechanisms enable organizations to detect anything that falls out of the scope of a user’s regular activity, e.g., failed log-ins, withdrawing an unusual amount or from an unusual location, etc. Upon discovering such suspicious activities or instances of unauthorized access, it would alert the user and authorities in real time, block suspicious transactions, and after several such transactions, even block the account.
The logs of users’ actions need to be easily accessible during a potential ‘post-mortem analysis’ when the team reviews an incident. They should provide the basis for a proper incident report, including the complete timeline, incident details, and root cause analysis.
Your company can leverage AI and ML to track, analyze, and manage the users’ activities. For instance, AI and ML algorithms can monitor patterns and discover anomalies in a user’s behavior 24/7.
Learn more: How to Use ML in Fraud Detection: Real-Life Examples and Emerging Trends
6. Encrypt sensitive data.
Fintech app owners need to protect their data at rest and especially in transition, when it’s easier to intercept. They are strongly recommended to encrypt sensitive data during transmission.
Encryption involves mathematical algorithms that convert data into code that makes sense only to the intended receiver. Unauthorized users or hackers cannot decipher it without the correct decryption key. Therefore, even if they hack the data, they won’t be able to access any sensitive information.
Mobile databases should also be encrypted to protect locally stored data. Pay special attention to the proper management of the encryption keys.
If your fintech app is going to operate under US legislation, it should encrypt the following sensitive information:
- Personal details a user provides to access a specific service or product, such as the name, social security number, address, contact numbers, and income information;
- Information that can be received from a transaction, i.e. credit card numbers, account numbers, payment history, credit card purchases, debit and credit information, and all kinds of transaction details;
- Any other information which can be obtained in connection with the delivery of certain financial services, e.g., a consumer report.
Secure data transmission demands using various encryption algorithms. Their paradigm shifts regularly because hackers succeed in cracking earlier encryption protocols.
You may choose between several industry-tested encryption algorithms available in the market.
AES (Advanced Encryption Standard)
AES encryption extends support to both hardware and software and is resistant to cryptanalytic attacks. Considered as one the safest algorithms out there, it’s used by the US Federal Government and, reportedly, half of Android and iOS apps.
TripleDES (Triple Data Encryption Standard)
What is triple encryption about? This algorithm divides data into 64-bit blocks and ciphers each data block three times. There are also three keys of 56 bit each, known as bundle keys. TripleDES is the preferred method for encrypting credit card PINs and other kinds of passwords. Flexibility and compatibility make it a good choice for dependent hardware encryption.
RSA
RSA assigns different keys for the encryption and decoding process. The encryption key is public, given to others, whereas the decryption key stays private. With the increased key size, the strength of the encryption increases. This algorithm is slightly slower than the others but is still suitable for small-scale fintech companies that deal with limited data transfers and processing.
Twofish
This open-source algorithm encrypts data into 128-bit blocks through 16 rounds of data encryption. Twofish is widely used for network applications with frequent key changes and apps with little or no RAM and ROM involvement.
7. Apply tokenization.
Tokenization is one of the safest methods of storing and transmitting sensitive data. It is basically replacing a piece of sensitive information that you want to protect, e.g., a customer’s credit card number, with a newly created random chain of symbols (token). Tokens are linked to the actual data in an encrypted way so that the original data can’t be reversed.
Only authorized users can decrypt the original information into a readable format. They need to access a unique database known as a ‘token vault’ that stores all the connections between the original data and the generated token. The token vault can be protected by database encryption to enhance the financial services application protection.
Tokens are generated for temporary use, preventing situations when someone can track sensitive data through transactions. Tokenization can be used with gift cards, NFC payments, online transfers, and so on.
Besides protecting data within organizations and online transactions, tokenization makes it easier to become PCI-compliant.

8. Secure APIs, cloud services, and servers.
Building a secure infrastructure is essential to fintech security. You will likely design, develop, and integrate application programming interfaces (APIs) that mobile and web apps use to interact with back-end information. Cyber-attackers frequently target them as potential weak links. However, back-end API security can ensure that there is no data leakage and all the users have sufficient space for storing their confidential data safely.
It’s recommended to limit the number of third-party integrations or build these components from scratch. If you need some complex functionality beyond your expertise, choose components from reliable partners and vendors. In the latter case, the team should start the monitoring and maintenance of integrations as soon as possible and constantly watch for service updates. Developers also need a plan of action in case a vulnerability is discovered.
API security requires the provision of identification, authentication, and authorization for accessing APIs. Use authentication tokens as well.
One of the best practices for API protection is implementing an automatic regular API token rotation, e.g., by implementing the OAuth 2.0 standard.
You can secure your APIs by the following means:
- Encrypt your data and use digital signatures
- Proactively identify and address API vulnerabilities
- Use quotas, throttling, and API gateways
Cybercriminals also tend to target fintech companies’ servers where they store user data, algorithms, security protocols, and other information. A compromised app can entail an attack on the server, and a compromised server can result in attacks on user devices and theft of their information. Consider the following security tips:
- Keep your OS updated. Fintech companies use a variety of operating systems on their servers for different purposes. These operating systems send regular security updates to users as new threats and security flaws are detected. Your tech team should ensure that these updates and patches are immediately applied on servers and run regular check-ups of all web server components. Hire a professional DevOps consultant if you need one.
- Choose what you save carefully. It’s best to keep the required minimum policy so as to install open ports or running services on the server. Office tools, utilities, and other non-essential software needn’t. They may contribute to security holes; their regular updates will add workload on the security team. For this reason, developers prefer command-line tools.
- Protect your web server. Maintain a separate drive to store web files, away from the OS, logs, and other system files.
- Develop a content security policy. CSP helps prevent cross-site scripting and data injection attacks. You can use signed cookies to limit access to content without changing its URL.
- Protect users’ data with an HTTPS SSL certificate. An SSL certificate ensures encryption of communication between the client browser/device and the application server. Nowadays, most popular browsers notify visitors if a site lacks a secure SSL connection. Thus, if you omit this step, your site may be deemed non-trustworthy.
Create special spaces to store data and documents safely. The app developers should also apply Transport Layer Security (TLS) to all traffic and continuously run vulnerability tests.
Integration of a virtual private network (VPN) can provide additional security. For example, it’s possible to make specific services, pages, and other app components accessible only from hardware that provides a valid public key. Unauthorized devices should be denied access and blocked with a system firewall, antivirus software, or any other program.
Firewalls and antivirus solutions also can work together for securing your fintech app. Modern firewalls thwart web-based malware and intrusion attempts and offer better inspection capabilities and control over individual applications in a network.
Market-leading antivirus solutions offer protection from viruses, spyware, malware, phishing attacks, intrusive ads, spam websites, and other online threats, while continuously upgrading their capabilities.
While building your fintech app’s infrastructure, you may also take advantage of cloud solutions.
Public cloud services may be unsuitable for hosting sensitive data. If your app runs on the public cloud, at least choose a reputable vendor who complies with modern cloud security standards. For example, many businesses utilize AWS enterprise cloud that helps minimize the impact of DDoS attacks and accelerates disaster recovery in case of disruptions.
An organization may host data with high-security requirements on a private cloud and the other data on a public cloud. In any case, it is imperative to safeguard the cloud servers against unauthorized users and third-party access.
Read also: How to create a micro investment app?
9. Organize safety-focused testing.
Fintech app security requires rigorous testing throughout the development life cycle and a few extra testing stages. The standard testing process should include seven consequent steps:
- Gathering requirements
- Requirements review
- Preparing all possible business scenarios that may result in an attack or data breach
- Functional testing, which may involve the exchange of money and personal information
- Database testing
- Security testing of APIs, identification, authentication, and authorization
- User acceptance, when the app’s core functions are tested from the user perspective
Here are some testing-related fintech app security best practices:
- Build or hire a professional security testing team. It would be best if you had vetted QA engineers who can create realistic data breach scenarios, introduce effective security management practices, and improve your code. They need to understand fintech sub-niches like insurance, banking, or investment to test the app’s user flows for security loopholes. A fast and cost-effective way to do it is to engage fintech security testers from an outsourcing vendor.
- Perform an IT security audit. This process can reveal technological flaws, weak encryption practices, and possible data storage issues, evaluate your compliance with fintech security standards, and verify the effectiveness of your security strategy.
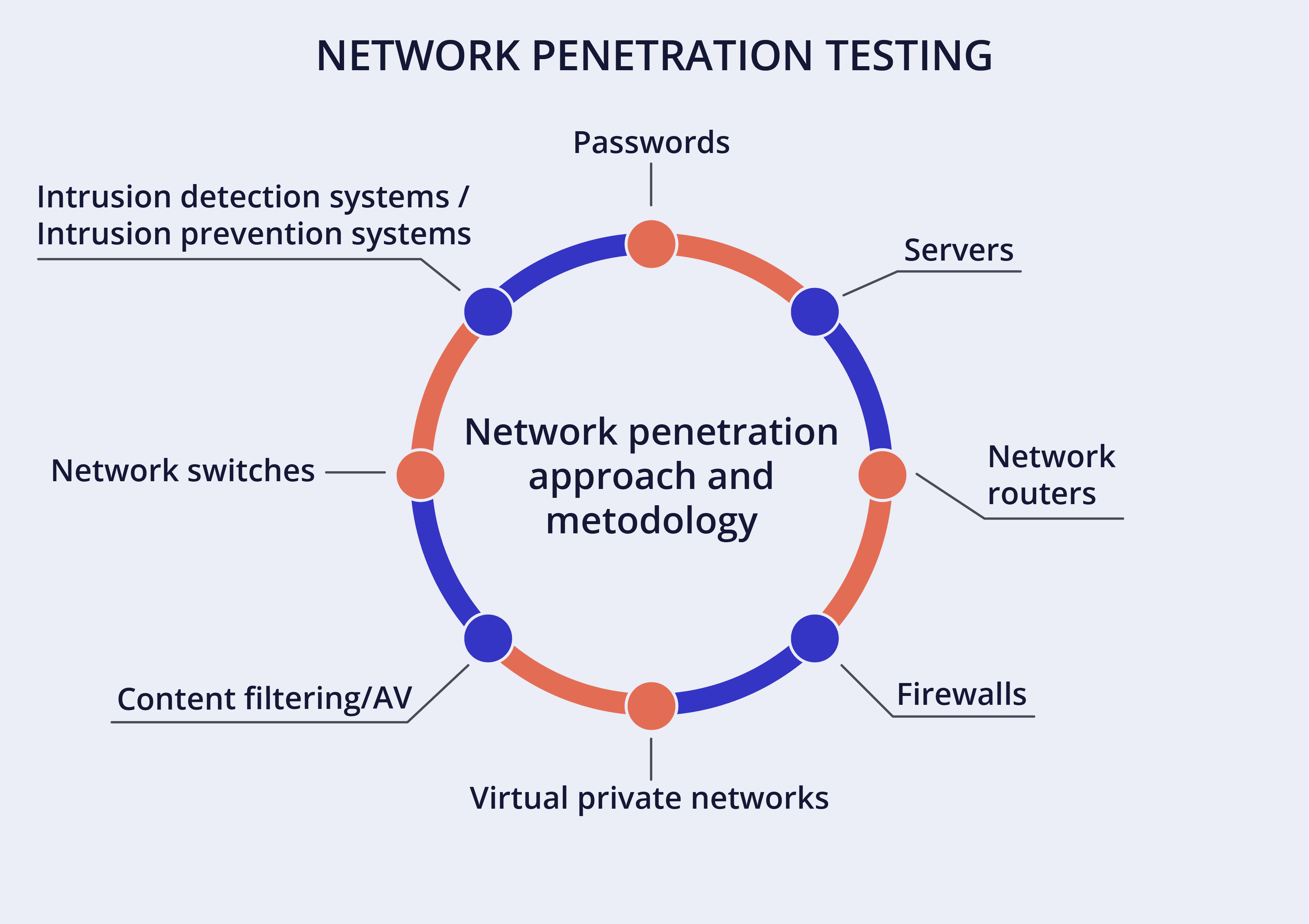
- Check network security. Test your servers, network devices, and DNS first. Inspect the servers, routers, firewalls, OS, databases, and file system for fintech storage.
- Run penetration tests. Faux attacks on your app can help you detect potential vulnerabilities and patch them up with attack-resistant code. When you simulate an attack and carry out the recovery process, remember to record everything. Specialized QA teams track key security metrics, such as server downtime, the presence of vulnerable data and other defects, and use the information to create a robust security policy for the organization.
- Examine everything from the client-side. During internal testing, an app is checked while it’s running in the browser. It may include JavaScript execution, HTML and CSS injection, clickjacking, and testing of the local storage. Such tests effectively detect vulnerabilities, identify potential harm, and assess the employees’ access rights. Double-check in real time all possible weaknesses in terms of authentication, authorization, session management, and fintech data security.
- Test your server security. See to it that the right frameworks and tools are in place. In the beginning, in-house security tests may suffice, but it’s best to have an independent security firm perform at least annual audits.
10. Integrate security in your daily workflows.
A company’s employees may be its biggest weakness when it comes to IT security. Careless or ill-informed employees, system misconfiguration, lost devices, or even accidental clicking on a malicious URL are just some of the ways to compromise the whole organization’s security.
Still, you can take some precautions to reduce the risks:
- There should be a detailed policy including the company’s data privacy and security provisions in place.
- It’s helpful to conduct security rehearsals at least once a year. The personnel would simulate possible attacks or other emergencies, act out ways to handle them, and then review the process and some key metrics (downtime, potentially lost data, etc.) to identify their fintech security issues.
- The software development process should proceed in separate development, pre-production, and production environments. Set up clear and coherent access rights. The pre-production and post-production stages are the higher management’s responsibility. Developers should have access only to the development stage and never meddle with business-critical data which becomes part of the app launching process at later stages.
- All employees, independent contractors, vendors, data-entry operators, and others involved in building and maintaining fintech solutions should sign non-disclosure agreements with your company.
- When accessing any back-office or development-related interface on your premises or remotely, the personnel should use only corporate hardware.
- Proper configuration of the routers will protect against internal attacks.
- Take precautions to ensure a fast and easy recovery. Your tech team should manage automatic regular backups of all critical data, files, and code. In the beginning, they may conduct backups every three months, but eventually, you may need to do it daily. It’s best to utilize an independent backup program allowing the choice of data to store and frequency. Alternatively, you can outsource the activity to backup experts.
- Fintech companies should be transparent about their security practices and educate their customers on the basic security best practices, such as:
- Shop only at official app stores
- Avoid using fintech apps on a public WiFi network
- Never save your username and password in the app
- Avoid rooting your Android devices because they can become vulnerable to viruses, spyware, and other threats
- What to do if the phone is lost or stolen
- Use VPN for extra security
- Install anti-virus software
...and so forth. Best practices and detailed tips should be easy to find on your company’s website. Regularly update your customers regarding their data and transactions security, ask for and analyze their feedback, and monitor their app usage habits and time.
Organizations are increasingly building real-time, proactive threat intelligence capabilities now. Regulations like GDPR mandate that businesses report a data breach within 72 hours, and early detection can help retrieve stolen credentials sooner.
Just like healthcare apps, modern fintech solutions have to embrace the “compliance-as-code” approach. It means integrating audits and compliance with regulations like PCI DSS and GDPR directly into their DevOps processes. Thus, they translate security controls into code and templates and break the silos between the information security, development, and operations teams.
Summing Up
Security and protection of the customers’ data should be at the forefront of fintech development; neglecting it can be devastating. A company’s data is also subject to data breaches and leaks.
This concern should permeate every step in the software development life cycle. Some of the ways to improve fintech security include:
- Minimalistic app logic and architecture
- Encryption and tokenization
- Code obfuscation
- Continuous monitoring and protection of the system’s servers, cloud services, and APIs
- The use of VPNs, firewalls, and antivirus solutions
- Rigorous security-focused testing
However, first and foremost, you need to hire the right staff for your project. Developing a secure fintech app requires diverse programming skills and considerable project management and information security efforts. Experienced developers are aware of all the technical challenges and fintech security standards imposed by various authorities and can realize effective solutions for the same on time and within budget.
Without the relevant expertise and skills on board, your project risks exceeding the budget, taking off too late, and eventually failing due to technical defects and non-compliance with national and international fintech security requirements.
Hundreds of companies from around the world have been outsourcing software development to Onix since 2000. We offer senior tech talent and product development expertise to build top-notch software, including sophisticated but reliable fintech solutions.
We can build a software platform from scratch or help improve your existing product at a reasonable price. Startups that look to hire remote developers for their projects are welcome too.
Do you need help or experts to protect your fintech app’s users and data? Just drop us a line!
Many thanks to Vitaliy Lavrinenko for the help with this article!
FAQ
Why should I protect my fintech app?
- Financial services deal with sensitive personal and business information that attracts cybercriminals.
- Fintech companies’ data is jeopardized by data storage issues, cross-platform malware contamination, and other vulnerabilities.
- The average cost of a financial services data breach is $5.97 million.
- It may take months to recover from damage caused by a cyberattack. If it results in the loss of sensitive information, the damaged reputation and legal and financial implications can be devastating.
- Startups face a higher risk due to limited human and capital resources.
How to protect finance apps?
The security of financial service apps is the collective responsibility of the financial company’s security officers, management, employees, software developers, and even users. The organization needs to take measures for data protection at all levels, such as:
- adopt public and internal security policies
- keep abreast with current security threats and developments in the industry
- сomply with the financial industry security standards
- conduct regular cybersecurity training for employees
- educate customers in preventing account takeover and other risks
- build the applications with cybersecurity in mind, and more
A fintech development agency like Onix can help you:
- with actionable advice on protecting your applications and customers
- by providing experienced fintech developers that know all the technical challenges and various security standards and can realize effective solutions
- through outsourced software development that adheres to all best practices
What are the primary security best practices for fintech application development?
- minimalistic app logic and architecture
- encryption and tokenization
- code obfuscation
- continuous monitoring and protection of the system’s servers, cloud services, and APIs
- the use of VPNs, firewalls, antivirus software, and other third-party fintech app security solutions
- rigorous security-focused testing